Azure AD SAML
This article will detail how you can use Azure SAML with your FTP Today account.
You will need two browser windows/tabs for these steps.
Create the Identity Service at FTP Today
Log into your FTP Today Site. Navigate to Settings > Authentication > Identity Service. Click on Add Service.

Enter a name for the New Service and select “Entra SAML” as the provider and Save.

Create the Application at Azure
On your FTP Today Site, locate the configuration information.

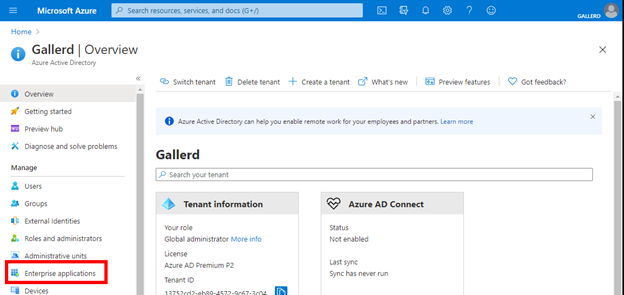
Log into your Azure portal and navigate to your Active Directory. Select Enterprise applications.
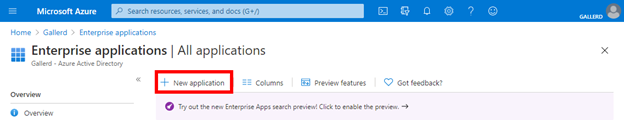
Select New Application.
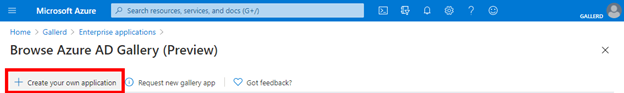
Select Create your own application
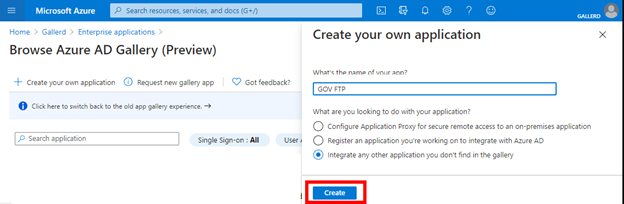
Enter a name for the application and Create.
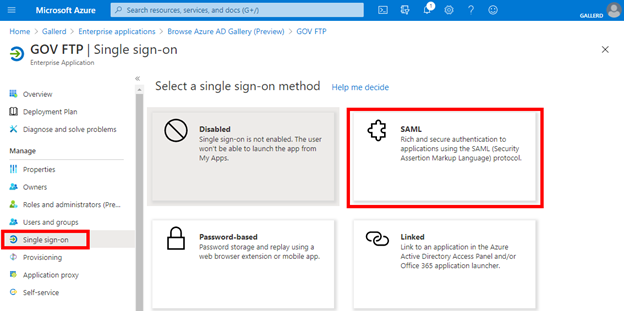
Select Single sign-on, then SAML.
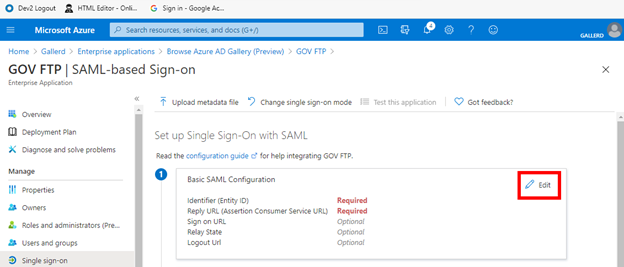
In the Basic SAML Configuration select Edit.
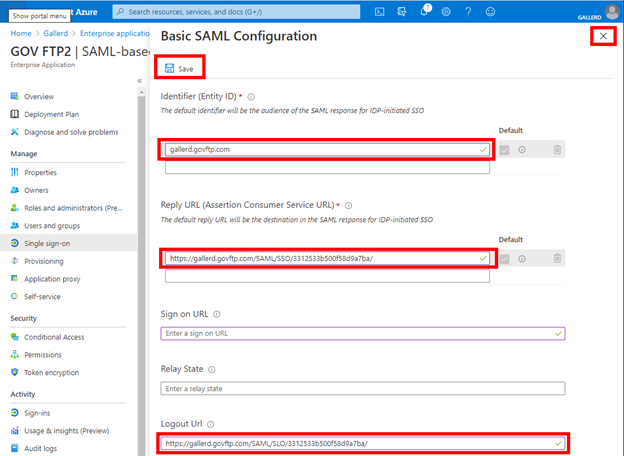
Copy the values from your FTP Today site to the corresponding fields at the Azure portal and Save and close the dialog.
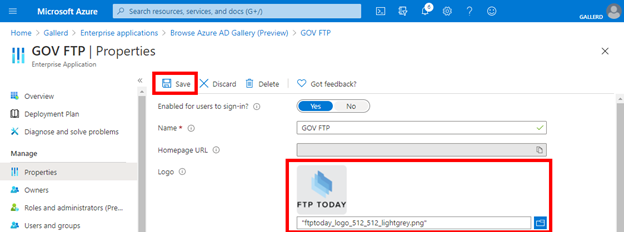
Download the logo from your FTP Today site. At Azure, select Properties, upload the logo and Save.
Configure the Identity Service at FTP Today
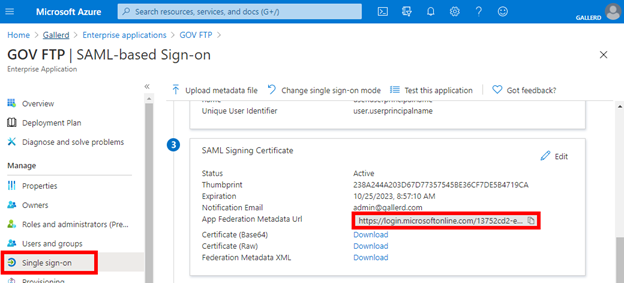
In the Azure portal, select Single sign-on. Locate the App Federation Metadata Url.
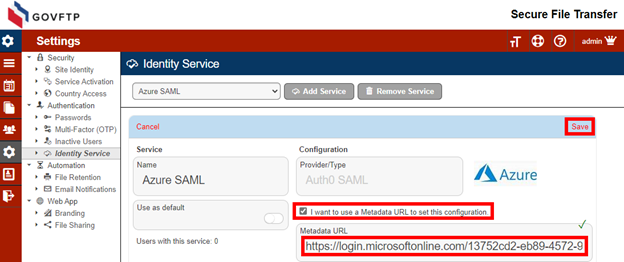
At your FTP Today Site, select “I want to use a Metadata URL”, copy the URL from Azure to your FTP Today Site and Save.
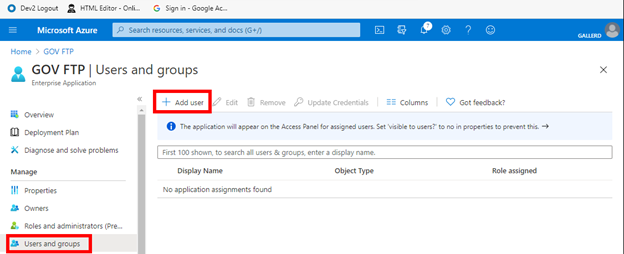
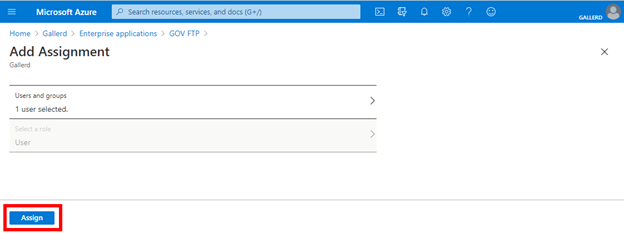
Assign the user to the application at Azure AD
In Azure AD, select Users and groups and then Add user.
Select Users and groups and then select the user to assign, then Select.
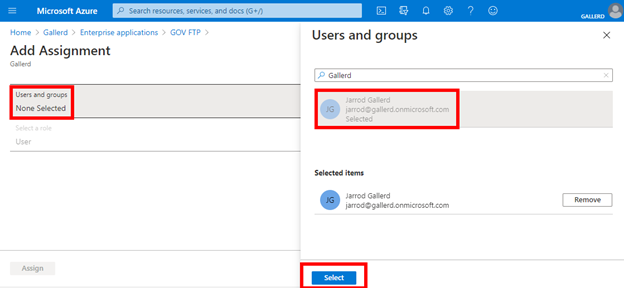
Select Assign.
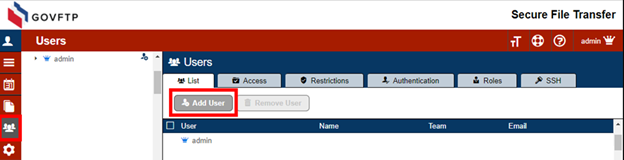
Add the user at FTP Today
In your FTP Today site, navigate to the Users area and select Add User.
Enter the username as set in the Azure AD service and select the Azure SAML service you created. Complete the rest of the fields as needed and Save.
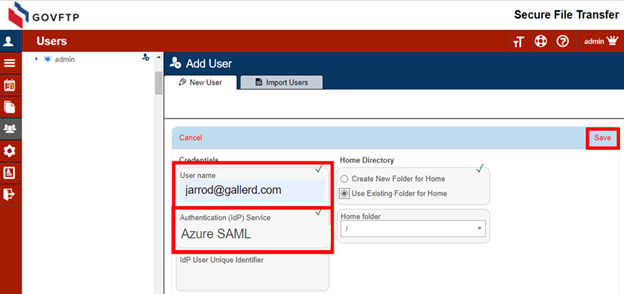
Azure AD supports an advanced security feature that offers further user verification. You may register the user with a unique identifier from Azure AD. In addition to matching the User Name to identify the user, we will match the Azure AD Object ID for that user.
When setting up the user, navigate to the user at Azure AD, select Profile and locate the Object ID. Copy that value.
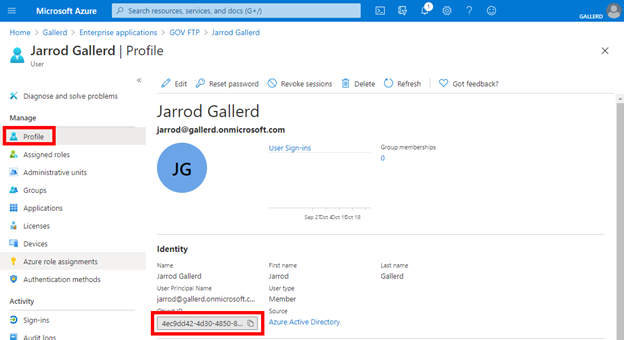
Include that value as the IdP User Unique Identifier when you create the user.
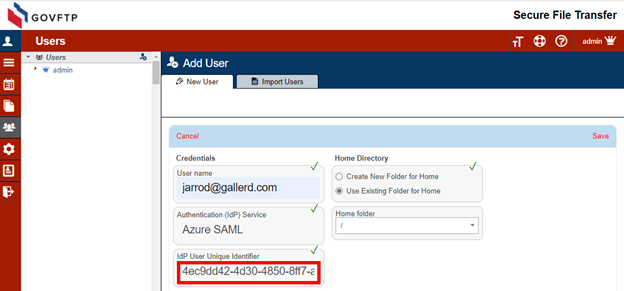
If the user already exists in your FTP Today site, you may change these settings on the Authentication tab for the user.
User access through FTP Today
Navigate to the site and enter the username and click Next.

There will be a brief “Authenticating” message.

If the user does not have an open session with Azure AD, they will have to authenticate.
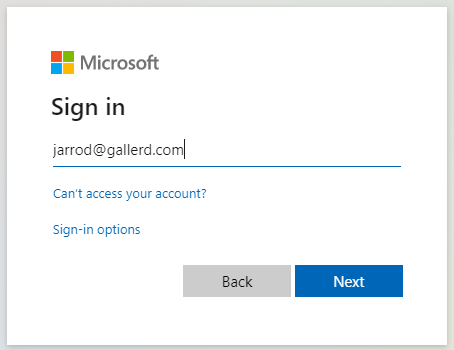
The user will now be logged into your FTP Today Site.
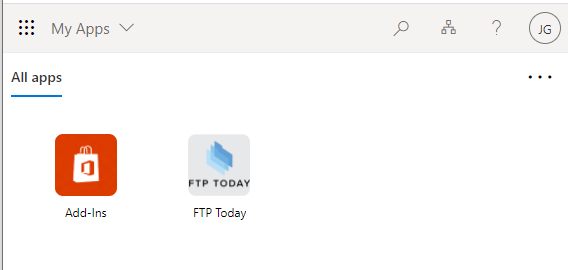
User access at Azure AD
Access the Microsoft My Applications portal. On the home screen, the user can click on the FTP Today application.
Ending the session
When done, the user may log out of the FTP Today site or allow the session to expire. This will not log the user out of Azure AD or any other services authenticated through Azure AD.
The user may also log out of Azure AD which will log the user out of your FTP Today Site. This will not close the browser window, but any action taken in the browser window will fail. After a short period, the browser window will reload to the login page.
The session timeout on the FTP Today Site may log the user out of the site even if they are still logged in at Azure AD. In that case, after reentering their username they will be immediately authenticated to the site.
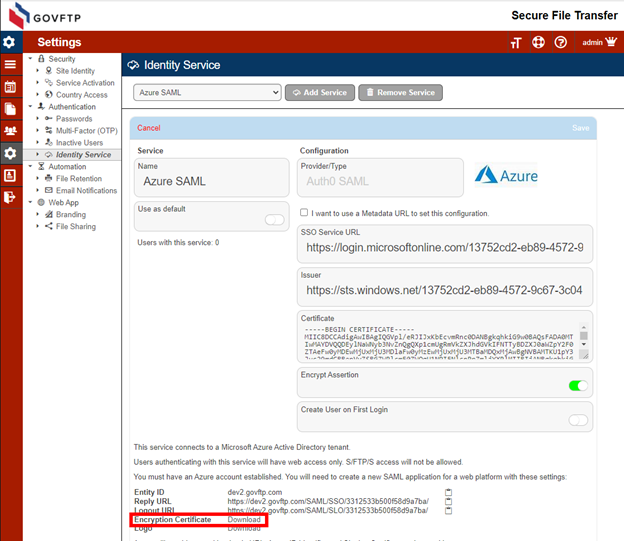
Encrypting the SAML response
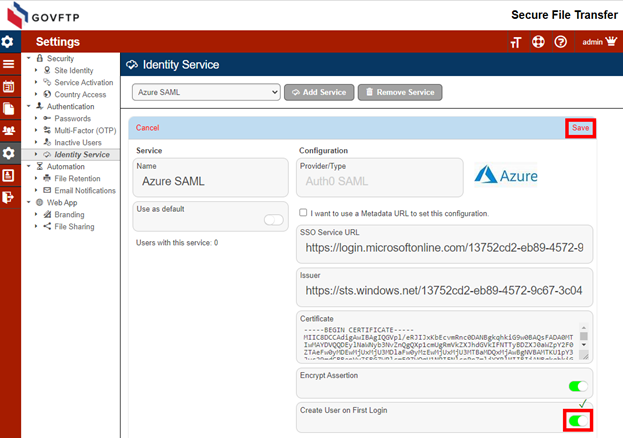
This is an advanced setting required for FIPS compliance. At your FTP Today Site, navigate to the Identity Service, toggle the “Encrypt Assertion” to on and Save.
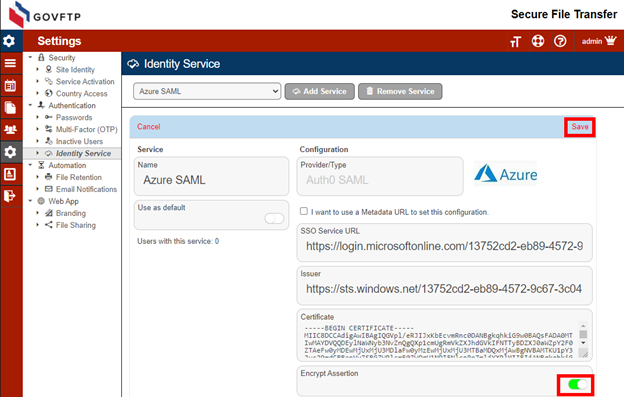
You will now see an Encryption Certificate link near the page bottom. Download the certificate.
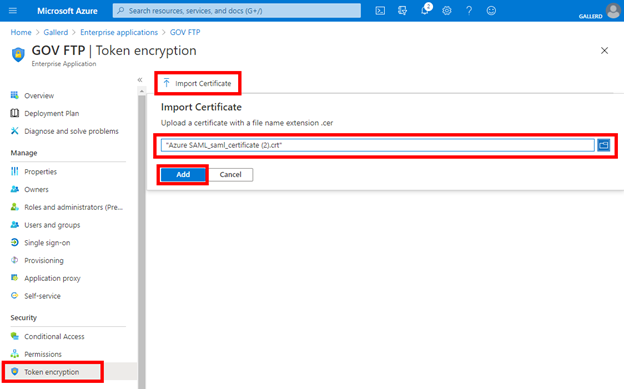
At your Azure AD site, navigate to the FTP Today application. Select Token encryption, then Import Certificate. Upload the certificate you downloaded and Add.
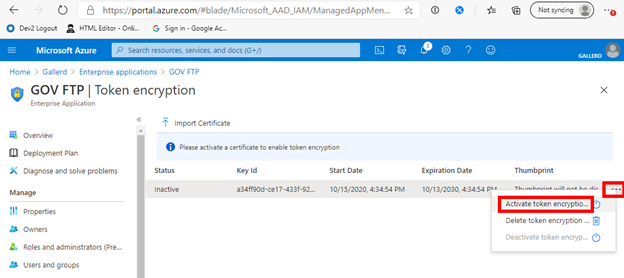
Select the context menu (ellipsis) and Activate token encryption.
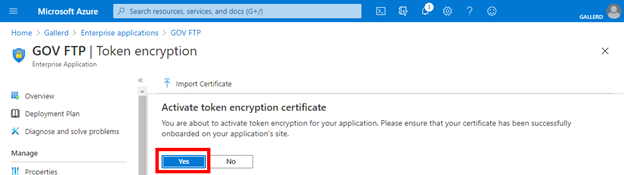
Confirm the activation.
Automatic User Provisioning
In your FTP Today Site, navigate to the configuration page for the Identity Service. Enable the “Create User on First Login” option and Save.
When the user logs into your FTP Today Site using the link from their “My Apps” page, the user will be automatically created. The user will have access to the site, but no permissions to files. You will need to give the user permission to the desired folders.
The user’s name and email will be populated with values provided from Azure AD.
%20Logos%202022/sharetru%20logo%20white%20bg%20and%20padding.png.png?width=400&height=100&name=sharetru%20logo%20white%20bg%20and%20padding.png.png)